Enhanced Due Diligence (EDD) Documentation Requirements 2026: What Regulators Check During Audits
Enhanced Due Diligence (EDD) documentation requirements include: enhanced identity verification records, source-of-funds and source-of-wealth evidence, UBO structure charts with supporting documents, sanctions and PEP screening logs, adverse media review records with source links, senior management approval records, and ongoing monitoring schedules with periodic review dates. All records must be complete, traceable, and retrievable on demand — regulators do not accept incomplete files or undate
Scoreplex
April 21, 2026 · 18 min read
Disclaimer
This information is for general purposes only and does not constitute legal or compliance advice. Consult a qualified professional for specific guidance.
Enhanced Due Diligence (EDD) documentation requirements include: enhanced identity verification records, source-of-funds and source-of-wealth evidence, UBO structure charts with supporting documents, sanctions and PEP screening logs, adverse media review records with source links, senior management approval records, and ongoing monitoring schedules with periodic review dates. All records must be complete, traceable, and retrievable on demand — regulators do not accept incomplete files or undated screenshots as evidence of compliance.
Passing an Enhanced Due Diligence (EDD) review is not the hard part. Proving you did it — to a regulator, six months later — is where most compliance teams run into trouble.
FATF Recommendation 10, EU AMLD6, and the US Bank Secrecy Act/FinCEN CDD Rule all share a common principle: institutions must not only conduct enhanced due diligence but document it in a way that can withstand scrutiny. The distinction matters. A thorough investigation that lives in an analyst's inbox or a series of disconnected spreadsheets is, from a regulatory standpoint, nearly indistinguishable from no investigation at all.
This article covers exactly what Enhanced Due Diligence (EDD) documentation regulators look for during audits: the seven document categories, what "audit-ready" means in practice, the most common gaps examiners flag, and how AI-native platforms are shifting the standard for what a complete EDD file looks like. If you are building or reviewing your documentation process, start with the complete guide to enhanced due diligence for regulatory context, then use this article as the documentation-specific reference.
Why Enhanced Due Diligence (EDD) Documentation Is Different From Standard KYC Records
Standard Customer Due Diligence leaves a relatively thin paper trail: a verified identity document, a confirmed address, a sanctions screen result. For most low-risk customers, that is sufficient. Enhanced due diligence operates under a different evidentiary standard entirely — and the documentation burden reflects that gap.
The core difference is not volume, it is depth of justification. Under Enhanced Due Diligence (EDD) regulatory requirements set by EU AMLD6 and FATF Recommendation 10, every material finding must be supported by a source, every judgment call must be explained, and every approval must be recorded with a timestamp and the name of the authorising officer. A Customer Due Diligence (CDD) file answers the questionwho is this customer? An EDD file answers the question why are we comfortable doing business with this customer despite elevated risk? — and it must answer that question with evidence, not assertion.
Regulators apply a straightforward test during examinations: if a compliance officer who had no involvement in the original case were handed the file today, could they reconstruct the full risk picture without asking a single follow-up question? If the answer is no, the documentation is incomplete — regardless of how thorough the underlying review actually was.
There is also a timing dimension. CDD is largely static: you collect it at onboarding and update it when something changes. Enhanced Due Diligence (EDD) is dynamic: it requires periodic review records, dated adverse media checks, updated screening results, and documented rationale every time the risk assessment is re-confirmed or revised. A file that was complete twelve months ago is not necessarily complete today.
This elevated standard applies equally to KYB documentation requirements when the subject is a legal entity. Corporate EDD files carry additional layers — ownership structure charts, beneficial ownership registers, multi-jurisdiction registry extracts — that have no equivalent in individual KYC. The sections below cover each document category in detail.
The 7 Categories of Enhanced Due Diligence (EDD) Documentation Regulators Expect
Every EDD file, regardless of jurisdiction or customer type, is built from the same foundational document categories. The following breakdown reflects the requirements of FATF Recommendation 10, EU AMLD6, and the FinCEN CDD Final Rule.
1. Enhanced Identity Verification Records
Beyond the standard identity document collected at CDD, EDD requires corroborating evidence from independent sources. For individuals, this typically means a government-issued photo ID cross-referenced against a biometric check and at least one additional source — a utility bill, a bank statement, or a verified registry entry — confirming the same name, address, and date of birth. For legal entities, it means certified copies of incorporation documents, current registry extracts confirming active status, and, where applicable, regulated-industry licences.
The key documentation requirement here is independence of sources. Two documents issued by the same institution, or two that ultimately trace back to the same underlying data source, do not satisfy the enhanced verification standard. Each source must be recorded with its full reference, retrieval date, and a link or copy of the original.
2. Source-of-Funds Evidence
Source-of-funds documentation establishes where the money used in the business relationship originates — not in general terms, but specifically. Acceptable evidence includes recent bank statements (typically three to six months), payroll records, business revenue documentation such as audited accounts or tax returns, or confirmation of a specific transaction origin such as a property sale or inheritance.
The file must record not only what evidence was collected but what conclusion was reached and why the compliance team found it credible. A bank statement alone is insufficient if the amounts are inconsistent with the stated business activity. The analyst's reasoning — why the evidence is proportionate and believable given the customer's profile — must be written into the file.
3. Source-of-Wealth Evidence
Source-of-wealth is distinct from source-of-funds and is one of the most commonly incomplete elements in EDD files. Where source-of-funds covers the specific transaction, source-of-wealth covers the accumulation of the customer's overall asset base. For high-net-worth individuals and PEPs, this distinction is critical under FATF Recommendation 12 and EBA Guidelines on ML/TF Risk Factors.
Acceptable documentation includes business ownership records with valuation evidence, inheritance documentation, investment account histories, or executive compensation records. Crucially, the file must record the basis on which the stated source of wealth was assessed as plausible — not simply that a document was received.
4. UBO Structure Charts and Supporting Documents
Beneficial ownership mapping is a mandatory component of EDD for corporate customers under AMLD6 and the FinCEN CDD Rule. The documentation requirement goes beyond knowing who the UBOs are: the file must contain a structure chart showing the full ownership chain, with percentage holdings at each layer, supported by official documents — registry extracts, shareholder registers, or notarised ownership declarations — for every entity in the chain.
Where ownership passes through jurisdictions with limited registry transparency, the file must record the steps taken to verify the structure, the sources consulted across each jurisdiction, and any residual uncertainty with a documented rationale for why the relationship was approved despite it.
5. Sanctions and PEP Screening Logs
Screening documentation must show three things: what lists were checked, when the check was run, and what the result was — including any hits reviewed and dismissed. A clean screening result recorded without a date is not audit-ready. A hit that was reviewed and cleared without a written rationale is a significant gap.
The file should record the screening platform or methodology used, the date and time of the search, the query parameters, the full result set including false positives reviewed, and — for any potential match — the documented reasoning for the disposition. Coverage must span the institution's required watchlist set: at minimum OFAC, UN Consolidated List, EU Consolidated List, and HMT, alongside any jurisdiction-specific lists applicable to the customer's operating countries.
6. Adverse Media Review Records
Adverse media documentation is where EDD files most frequently fail examinations — not because the searches were not conducted, but because the record does not demonstrate a credible, structured review. Simply attaching a Google search screenshot with no date, no query terms, and no analyst commentary does not meet the evidentiary standard.
A compliant adverse media record includes: the date the search was conducted, the search terms and sources used, a summary of material findings with direct links to original sources, a categorisation of each finding by risk type (financial crime, regulatory sanction, reputational risk), and a documented conclusion explaining why identified items were assessed as material or dismissed. For high-risk customers, the file should also show the time elapsed since the last adverse media review and confirm it falls within the institution's approved monitoring frequency.
7. Senior Management Approval Records
For customers that trigger EDD — PEPs, high-risk jurisdiction connections, complex ownership structures — FATF Recommendation 12 and AMLD6 both require that the business relationship is approved by senior management, not simply by the front-line compliance analyst. This approval must be documented.
The record must show: the identity and role of the approving officer, the date of approval, a summary of the risk factors that triggered EDD, and confirmation that the approver reviewed the completed file before signing off. An email chain is technically a record, but it creates retrieval and traceability problems at scale. Institutions that handle significant EDD volumes need this approval integrated into the case management workflow — with a timestamped, named sign-off that is part of the file itself, not stored separately.
What Must an Ongoing Monitoring Record Show?
Collecting EDD documentation at onboarding is necessary but not sufficient. FATF Recommendation 10 explicitly requires enhanced ongoing monitoring for high-risk relationships — and regulators treat the monitoring record as a separate, equally important part of the EDD file. An otherwise complete onboarding file with no evidence of subsequent review is a gap, not a minor administrative oversight.
A compliant ongoing monitoring record must show four things: that a review was scheduled, that it was conducted on time, what was reviewed, and what conclusion was reached.
Review frequency must be risk-based and documented. There is no universal interval mandated by regulation, but the institution's own risk appetite framework sets the standard against which regulators will measure compliance. Typical structures used in practice are:
- High-risk / PEP relationships: quarterly or semi-annual review, with event-triggered reassessment when material new information emerges
- Elevated-risk relationships: annual review as a baseline, with triggers defined for interim escalation
- Ongoing transaction monitoring: continuous, with periodic reconciliation against the EDD risk profile on a schedule proportionate to transaction volume and complexity
What the review record must contain: the date the review was conducted, the name and role of the analyst who performed it, a confirmation that all seven document categories above were checked for currency, an updated adverse media search with the date and query parameters logged, a re-run of sanctions and PEP screening with results documented, and a written conclusion confirming whether the risk assessment remains unchanged or has been revised. If the risk rating changes, the file must record the trigger, the new rating, and any escalation steps taken — including, where required, fresh senior management sign-off.
Event-triggered reviews are equally important and frequently missing from EDD files. Under the EDD regulatory requirements set by EU AMLD6 and the EBA Guidelines on ML/TF Risk Factors, institutions must have defined triggers that initiate an out-of-cycle review — adverse media hits, significant changes in transaction behaviour, changes in UBO structure, or a counterparty appearing on a new sanctions list. The file must show that the trigger was identified, that a review was initiated within the institution's defined response window, and that the outcome was documented with the same rigour as a scheduled review.
A monitoring schedule that exists in a policy document but leaves no trace in individual case files provides no regulatory protection. The FinCEN CDD Final Rule makes clear that ongoing monitoring obligations attach to the relationship, not just to the onboarding event — and the documentation standard is the same throughout.
What Does "Audit-Ready" Actually Mean for an Enhanced Due Diligence (EDD) File?
The phrase appears in regulatory guidance and internal compliance frameworks with enough frequency that it risks becoming meaningless. In practice, regulators apply three concrete criteria when they open an EDD file during an examination. A file is audit-ready when it satisfies all three — not just one or two.
Completeness. Every required document category is present and accounts for the current state of the relationship, not the state at onboarding. A source-of-funds assessment that was accurate three years ago but has never been revisited is incomplete by the standard of ongoing monitoring. An adverse media record that covers the entity but not its directors — where directors are a named risk factor in the institution's own risk assessment — is incomplete. Completeness is measured against the risk profile that triggered EDD in the first place: the higher the risk, the more granular the documentation standard.
Traceability. Every finding, conclusion, and approval decision can be traced back to a specific piece of evidence with a clear chain of custody. This means documents are dated, sourced, and linked to their original location. A screening result shows which list was checked, on which date, using which query. An adverse media finding includes the URL or document reference of the original source — not a paraphrase, not an analyst's summary alone. An approval decision shows which officer approved it, in what capacity, and on what date. If any step in the chain requires a follow-up call to an analyst to explain what happened, the file is not traceable.
Timeliness. Every element of the file reflects the current risk picture within the institution's defined review window. An adverse media check dated fourteen months ago, in a relationship flagged as high-risk with a six-month review cycle, is not timely — and a regulator will treat it as an active gap, not a historical one. Timeliness also applies to the response to triggers: if an event-triggered review was due within five business days of a sanctions list change and the file shows it was completed twelve days later, the delay must be explained.
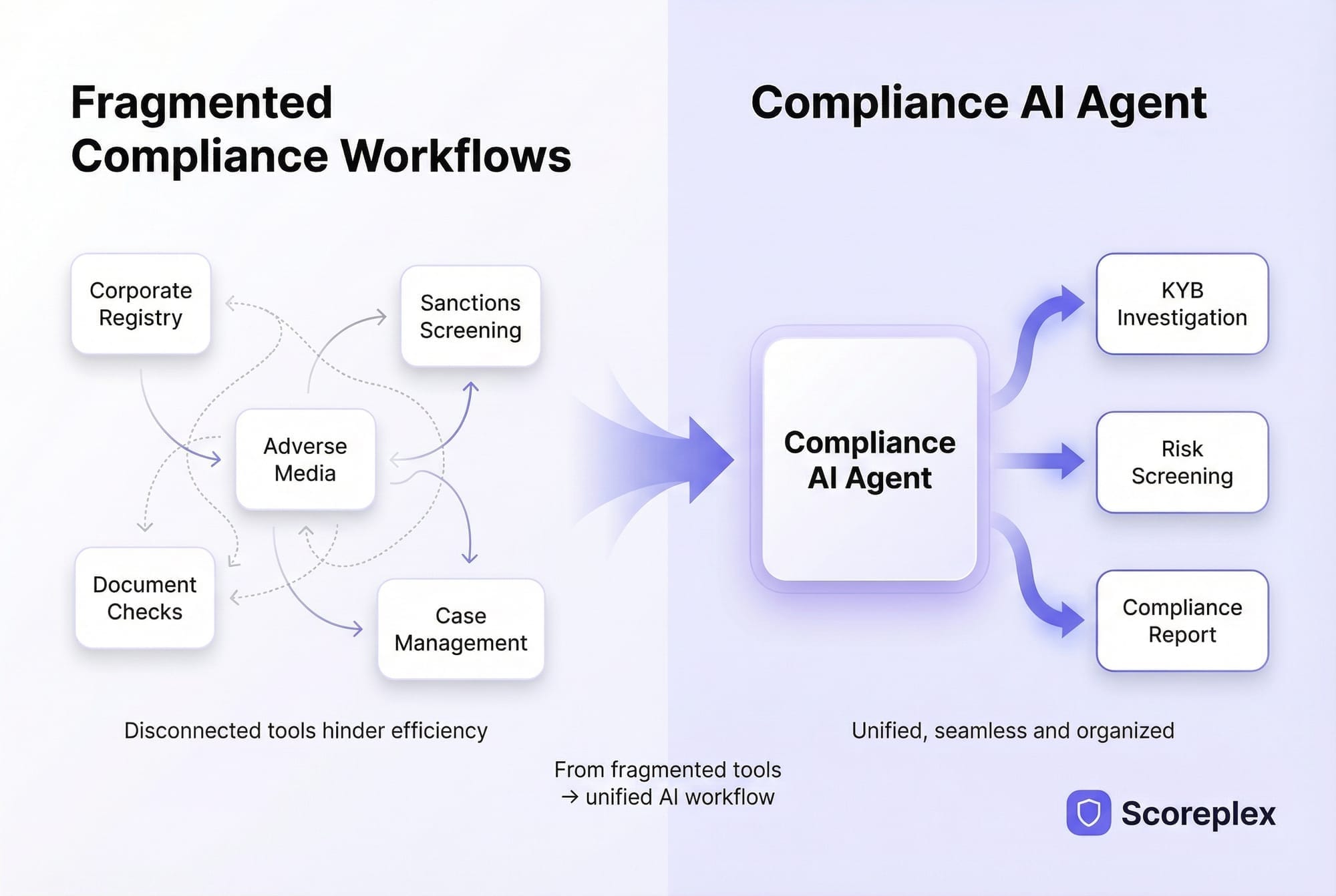
These three criteria apply equally to manually assembled files and to files generated by automated platforms. The difference is that manual assembly creates structural conditions that make completeness, traceability, and timeliness difficult to maintain at scale. Analysts working across multiple tools — registry portals, screening platforms, news aggregators, email — must actively reconstruct the file each time. A missing date, a broken link, or an undocumented dismissal of a false positive is not negligence; it is the predictable output of a fragmented process.
This is the documentation gap that regulators encounter most consistently, and it is the reason the EDD checklist approach — where each step generates its own record as a structural byproduct of the process — produces more reliable audit outcomes than retrospective file assembly. When a compliance team is asked to conduct enhanced due diligence at volume, the documentation standard does not change — but the process must be designed to meet it consistently, not case by case.
What Documentation Gaps Do Regulators Flag Most Often?
Regulatory examination findings across EU, UK, and US jurisdictions point to a consistent set of recurring documentation failures. These are not edge cases. They appear in enforcement actions, thematic reviews, and supervisory feedback letters with enough regularity that compliance teams can treat them as a practical checklist of what not to leave unresolved before an audit.
1. Source-of-wealth rationale is absent or conclusory.
The most frequently cited gap in EDD files reviewed by the EBA and FCA is a source-of-wealth section that states a conclusion without supporting it. Entries such as "customer confirmed wealth derived from business activities" or "source of wealth verified" with no underlying document, no named business, and no cross-reference to corroborating evidence do not satisfy the standard set by the EBA Guidelines on ML/TF Risk Factors. A compliant record names the specific source, identifies the document that evidences it, and explains why the compliance team found the explanation credible given the customer's overall profile. Assertion is not evidence.
2. Adverse media searches are undated or show no query parameters.
A search result with no date is functionally useless to a regulator. Without a date, there is no way to assess whether the search falls within the required monitoring window, whether it predates a material event, or whether it was conducted at all rather than reconstructed after the fact. Equally problematic is a search record that shows a result summary but does not document the query terms used — different query constructions produce materially different result sets, and the absence of query documentation means the search cannot be independently replicated or assessed for adequacy. Every adverse media record must show: the date, the sources searched, the exact query terms, the full result set including dismissed items, and the analyst's written disposition of each material hit.
3. UBO structure charts are present but unsupported.
A beneficial ownership diagram that shows a three-layer holding structure is a useful starting point — but regulators expect each node in that structure to be supported by a document. A box labelled "Holding Co. — British Virgin Islands — 60% owner" with no registry extract, no shareholder register, and no notarised declaration is an unverified assertion in diagrammatic form. Under FATF Recommendation 10 and the FinCEN CDD Final Rule, UBO identification requires documentation, not just mapping. Where registry access is limited by jurisdiction, the file must record what steps were taken to verify ownership through alternative sources and acknowledge any residual uncertainty with a written risk-acceptance rationale.
4. Screening logs show hits with no documented disposition.
A sanctions or PEP screening result that flags a potential match and then shows nothing further is one of the most serious documentation gaps an examiner can find. It creates an evidentiary vacuum: the institution identified a possible risk and left no record of what it did with that information. Every potential match — including those ultimately assessed as false positives — must have a written disposition. The record must show who reviewed the hit, what information was used to assess it, what conclusion was reached, and on what date. A false positive dismissed without documentation is indistinguishable from a true match that was ignored.
5. Senior management approval is missing or cannot be attributed.
For relationships that required senior management sign-off under AMLD6 or the institution's own EDD policy, the file must contain an approval record that identifies the approving officer by name and role, not simply by initials or a generic "approved" stamp. Email approvals stored outside the case file are a systemic retrieval problem — during an examination, if the approval cannot be produced as part of the file, it may as well not exist. Institutions handling EDD at volume consistently find this gap at the point where the compliance workflow hands off to relationship management: the risk assessment is complete, but the formal sign-off never makes it back into the documented record.
Each of these gaps shares a common root cause. They are not failures of investigation — in most cases the underlying review was conducted adequately. They are failures of documentation discipline, and they occur most consistently in environments where the EDD process and the documentation process are treated as separate activities rather than as a single integrated workflow. The next section covers how that structural problem is addressed at the platform level.
How AI Generates Audit-Ready Enhanced Due Diligence (EDD) Documentation Automatically
The documentation gaps described in the previous section are not primarily a training problem or a resource problem. They are a process architecture problem. When an analyst conducts EDD across five or six separate tools — a registry portal, a sanctions screening platform, a news aggregator, a shared drive, an email thread — the documentation of each step is a manual, retrospective activity that competes with the next case in the queue. At volume, something gets missed. The question is not whether, but which case and which element.
AI-native Enhanced Due Diligence (EDD) platforms address this at the structural level by making documentation a byproduct of the investigation itself, not a separate task that follows it.
Every step generates its own record. When an EDD AI agent retrieves a registry extract, it logs the source, the retrieval timestamp, and the data returned — automatically, as part of the same operation. When it runs a sanctions and PEP screen, the full result set, the lists checked, the query parameters, and the date are written into the case file without analyst intervention. When it conducts an adverse media review, it clusters results by event, deduplicates syndicated coverage, and records both the dismissed items and the rationale for dismissal as structured data — not a screenshot, not a summary in a notes field.
The result is a file that satisfies the three audit-ready criteria by construction: complete because the workflow itself enforces completeness at each step; traceable because every finding links directly to its primary source; timely because monitoring schedules are built into the case management layer and trigger automatically rather than depending on calendar reminders.
The documentation quality gap between manual and AI-assisted Enhanced Due Diligence (EDD) is measurable. Manual EDD costs $10–80 per case and takes 30–240 minutes of analyst time. AI-assisted EDD costs $2–5 per case and completes in 5–30 minutes. The cost and time reduction is significant — but for compliance teams facing an audit, the more operationally relevant difference is in the audit trail. Manual processes produce files assembled from multiple sources after the fact, with the quality variability that entails. AI-native platforms produce a single structured narrative per case, with source links, timestamps, and disposition records built in as standard output.
The false positive problem in adverse media — one of the five documentation gaps regulators flag most consistently — is directly addressed by AI clustering and deduplication. Manual adverse media searches return up to 90% false positives: name collisions, duplicated syndications, outdated allegations that have no bearing on the current risk assessment. Without AI, every one of those false positives either consumes analyst time to document and dismiss, or — more commonly at scale — gets left in the file undocumented, creating exactly the kind of gap described in the previous section. AI reduces false positives by 85%, which means fewer irrelevant entries in the file, faster review cycles, and a cleaner audit trail that reflects genuine risk findings rather than noise.
For compliance teams operating across multiple jurisdictions, coverage consistency is an additional documentation requirement that manual processes struggle to meet. Scoreplex operates across 140+ business jurisdictions, screens against 325+ global watchlists, and processes documents in 200+ languages — ensuring that a cross-border EDD case produces documentation that covers the full jurisdictional footprint of the entity under review, not just the registries the analyst happened to have access to that day.
At 500 cases per month, the direct cost saving from AI-assisted EDD exceeds $219,000 annually. The avoided regulatory exposure from consistent, complete, audit-ready documentation does not have a published price — but the $6.6 billion in AML/KYC fines issued globally in 2023 provides useful context for how regulators price documentation failures when they find them.
Conclusion
Enhanced Due Diligence (EDD) documentation is not a compliance formality that follows the real work of due diligence — it is the work, from a regulatory standpoint. A thorough investigation that cannot be reconstructed from the file is, in the eyes of an examiner, an investigation that did not happen. The seven document categories covered in this article, combined with a monitoring record that meets the completeness, traceability, and timeliness criteria, define the minimum evidentiary standard that regulators apply when they open a case file during an audit.
The firms that consistently pass examinations without material documentation findings are not necessarily doing more thorough investigations than their peers. They have built processes where documentation is a structural output of each investigative step, not an administrative task performed afterward. At the case volumes most financial institutions operate at today, that distinction determines whether an EDD programme is defensible or merely credible in intention.
For teams evaluating whether AI-assisted workflows can close the structural gaps described in this article, book a demo to see how Scoreplex generates audit-ready EDD files as a standard output of the investigation process.
Frequently Asked Questions
Q1: What documents are required for enhanced due diligence (EDD)?
Enhanced due diligence documentation requirements cover seven categories: enhanced identity verification records from independent sources, source-of-funds evidence, source-of-wealth evidence, UBO structure charts with supporting documents for each ownership layer, sanctions and PEP screening logs with dated results and hit dispositions, adverse media review records with source links and analyst commentary, and senior management approval records with named sign-off. All records must be retrievable on demand and reflect the current state of the relationship, not only the state at onboarding.
Q2: How long must Enhanced Due Diligence (EDD) records be retained?
Retention requirements vary by jurisdiction. Under EU AMLD6, EDD records must be retained for a minimum of five years from the end of the business relationship or the date of the occasional transaction. UK Money Laundering Regulations require the same five-year minimum. US BSA/FinCEN requirements mandate retention of CDD and EDD records for five years from the date the record was created. Some jurisdictions permit or require extensions beyond five years for relationships that were subject to suspicious activity reporting. Institutions operating across multiple jurisdictions should apply the most stringent applicable retention standard across their entire EDD file set.
Q3: What is the difference between Enhanced Due Diligence (EDD) documents and standard KYC records?
Standard KYC records establish identity and confirm a customer meets baseline onboarding requirements. EDD documentation goes further: it must evidence the institution's risk assessment reasoning, not just the data collected. This means every material finding requires a sourced document, every judgment call requires written rationale, and every approval decision requires a named, dated sign-off from a sufficiently senior officer. EDD files also require ongoing monitoring records — dated periodic reviews and event-triggered reassessments — that have no equivalent in standard KYC documentation.
Q4: What do regulators check during an Enhanced Due Diligence (EDD) audit?
During an EDD examination, regulators typically assess whether the institution correctly identified the EDD trigger, whether all seven document categories are present and current, whether adverse media searches are dated and show query parameters, whether UBO structure charts are supported by primary source documents, whether screening logs show full result sets including dismissed hits, whether senior management approval is documented and attributable, and whether the ongoing monitoring schedule has been followed with records to prove it. The most common findings involve missing source-of-wealth rationale, undated adverse media searches, and screening hits with no documented disposition.
Q5: What are KYB documentation requirements for Enhanced Due Diligence (EDD)?
KYB documentation requirements for EDD encompass all seven standard categories, with additional corporate-specific elements. Entity identity verification requires certified registry extracts and incorporation documents, not just a company number. UBO mapping must cover the full ownership chain across all jurisdictions, with supporting documents at each layer. Where the entity operates in a regulated industry, current licence documentation must be included. Corporate EDD files also require documentation of the entity's controllers and authorised signatories as distinct from its beneficial owners, particularly where those roles are held by different individuals.
Q6: How does AI improve Enhanced Due Diligence (EDD) documentation quality?
AI-native EDD platforms improve documentation quality by making it a structural output of the investigation process rather than a retrospective manual task. Each step — registry retrieval, sanctions screening, adverse media analysis — automatically generates a dated, sourced record as part of the same operation. This eliminates the documentation gaps that arise when analysts work across multiple disconnected tools and assemble the file afterward. AI also reduces adverse media false positives by 85%, which means fewer undocumented dismissed hits in the file — one of the most consistently flagged gaps during regulatory examinations. The output is a single structured narrative per case with source links, timestamps, and disposition records built in as standard.
Q7: What happens if Enhanced Due Diligence (EDD) documentation is incomplete during a regulatory audit?
Incomplete EDD documentation during a regulatory examination can result in a range of supervisory outcomes depending on the jurisdiction, the severity of the gaps, and the institution's overall compliance record. At minimum, examiners will issue findings requiring remediation within a defined timeframe, with follow-up verification. More significant gaps — particularly those involving missing senior management approvals, undocumented screening hits, or systematic absence of source-of-wealth evidence — can result in formal enforcement action, financial penalties, and mandated independent compliance reviews. In jurisdictions that apply a strict liability standard to AML documentation failures, the absence of a record can be treated as evidence that the required step was not taken, regardless of what actually occurred.